iPod to iRobot: How Our Loyal Devices Are Turning Against Us
The Internet of Things is being used as a weapon. Don't turn your back on your DVR.
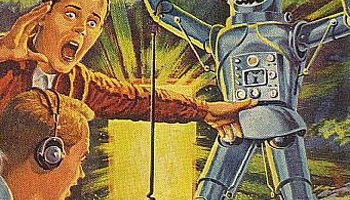
Robots run amok is a common science fiction trope: anthropomorphic terrors turning against their masters. Few versions of that story have the antagonists looking like printers. With the growing Internet of Things (IoT), however, that is quickly becoming our new reality.

![XYZ [2]](http://blogs-images.forbes.com/briansolomon/files/2016/10/Screen-Shot-2016-10-21-at-12.39.17-PM1.jpg?width=960)
These types of attacks have historically come from desktop and laptop computers, but recent attacks have increasingly come from internet peripherals. The Mirai software targets these unprotected devices and slaves them to a botnet that can be accessed and used at any time, for intimidation, entertainment, or even profit: oftentimes the groups responsible will rent out botnet time at affordable rates to anyone with bitcoin to spare. [4]
The October attacks were just the most recent iteration of a growing trend. Over the summer, security firm Sucuri discovered a botnet of 25,000 cameras that was assaulting a brick-and-mortar jewelry store, with unknown motivations. [5] In September, the hosting giant OVH came under several attacks with volumes thought to be logistically nearly impossible (with traffic exceeding 1 terabit per second from over 145,000 devices). [6] That same month, a prominent security journalist named Brian Krebs came under attack numerous times before his website was eventually booted by the security firm he had been using, Prolexic. The company could no longer afford to protect him from the high volumes of attacks. [7]
The fact that these attacks were made possible by the proliferation of internet-connected but undersecured devices has vast implications. Political activists in countries hostile to free speech have had their work censored for decades, but now those wishing to censor individuals need not be in positions of power or even possess a great deal of technical knowledge, since the Mirai source code is freely available to all, and there are more internet-connected devices than ever. Attacks can come from anywhere in the world to anywhere in the world and differentially impact independent and underfunded bloggers and journalists who face expulsion from hosting services that are understandably unwilling to shoulder the burden of being routinely crippled. We face a new threat of internet bully that is anonymous, ubiquitous, and available for hire.
Enter Google. Through one of their subsidiaries, Jigsaw, they have recently released a new type of infrastructure to protect these websites and authors. Originally intended for “small, under-resourced news sites”, Google has recently opened its infrastructure to any “independent news site” – those not owned by a particular government or political party – that wishes to join. [8]
The initiative is built off of Google’s Pagespeed service, which is a front-end tool that was originally oriented to allow developers faster page load times. Sites wishing to join Project Shield would sit behind this structure and would take advantage of Google’s massive scale: unless the attack were strong enough to bring down the entire service, they can’t touch any individual site. While this isn’t a wholly new model (see Cloudfire) this is the first time the service has been offered for free and with the intent of protecting free speech. [9]
Google has maintained there is no monetary incentive here, with Jigsaw president Jared Cohen stating: “This isn’t about revenue… you have to make sure that once people have access to the information, it doesn’t get DDOS attacked, it doesn’t get compromised, it doesn’t get censored in a politically motivated way.” [10] Google’s incentives may not include a direct dollar exchange, but their entire business model is predicated on having people feel comfortable sharing their information online. The majority of Google’s products – Google Search, Gmail, Cloud Services – survive only to the degree that we as consumers of information are willing to provide and share our content with one another – and with Google. In order to protect this ecosphere, Google may need to continue to add cost and complexity to its operating model by introducing products such as Project Shield. But Google should take this further: they should use their immense scale and market position to push for changes to IoT regulations and mandate more stringest minimum security thresholds on internet-connected devices. Concurrently, they should aim to make the public more aware of this issue and the steps they can take to avoid having devices they own be part of a botnet bully.
Word Count: 798
Sources
[1] Canon, (2016), Available at: http://www.canon.com [Accessed 18 November 2016].
[2] Forbes, (2016), Internet Outage Map [ONLINE]. Available at: http://www.forbes.com/sites/briansolomon/2016/10/21/hacked-cameras-cyber-attack-hacking-ddos-dyn-twitter-netflix/#5f124afb7e6f [Accessed 18 November 2016].
[3] Dots left to right represent requests on the server, with the bar on the right attempting to service as many requests as possible. Traffic is directed against one particular file, locking up the resources of the target and crashing the system.
[4] Thomas Fox-Brewster. 2016. How Hacked Cameras Are Helping Launch The Biggest Attacks The Internet Has Ever Seen. [ONLINE] Available at: http://www.forbes.com/sites/thomasbrewster/2016/09/25/brian-krebs-overwatch-ovh-smashed-by-largest-ddos-attacks-ever/#56bd8adb6fb6. [Accessed 18 November 2016].
[5] Dan Goodin. 2016. Large botnet of CCTV devices knock the snot out of jewelry website. [ONLINE] Available at: http://arstechnica.com/security/2016/06/large-botnet-of-cctv-devices-knock-the-snot-out-of-jewelry-website/. [Accessed 18 November 2016].
[6]Dan Goodin. 2016. Record-breaking DDoS reportedly delivered by >145k hacked cameras. [ONLINE] Available at: http://arstechnica.com/security/2016/09/botnet-of-145k-cameras-reportedly-deliver-internets-biggest-ddos-ever/. [Accessed 18 November 2016].
[7] Dan Goodin. 2016. Why the Silencing of KrebsOnSecurity Opens a Troubling Chapter for the Net. [ONLINE] Available at: http://arstechnica.com/security/2016/09/why-the-silencing-of-krebsonsecurity-opens-a-troubling-chapter-for-the-net/. [Accessed 18 November 2016].
[8] Andy Greenberg. 2016. Google Wants to Save News Sites From Cyberattacks—For Free. [ONLINE] Available at: https://www.wired.com/2016/02/google-wants-save-news-sites-cyberattacks-free/. [Accessed 18 November 2016].
[9] Russell Brandom. 2013. Google Launches New Anti-DDOS Service Called Project Shield. [ONLINE] Available at: http://www.theverge.com/2013/10/21/4862724/google-launches-new-anti-ddos-service-called-project-shield. [Accessed 18 November 2016].
[10] See [8]



Great post, Will! I, too, touched on cyber security as it relates to IoT in my post on smart refrigerators. One thing that is particularly concerning to me in addition to what you’ve laid out in your post is the potential for amplification as more and more devices are connected. Years ago, if you got a computer virus, it was fairly contained to your PC. In today’s world, if you have many “smart” devices connected in your home, a Mirai attack could penetrate throughout many devices. This becomes particular concerning if you have devices related to medicine (e.g. monitors) in your home’s connected ecosystem. One of the biggest problems that hopefully Google and/or the technology provides will address in the immediate future is finding ways to make these IoT devices more secure and ensuring they always have the latest software updates to protect against known issues. If you have connected devices that you don’t access often, it’s likely that you’ll fall behind on software updates unless they can be pushed automatically. I’ll be very curious to see how this space evolves in the coming years, and agree that companies like Google should lead the charge here.
While its great that google is providing infrastructure to protect news publishers. Wouldn’t be better to figure out a way to secure all of the connected devices? This may fall on the device manufacturer or perhaps these devices should be behind a service like amazon IOT. What do you think is the best way to prevent this in the future?
Any idea what the legal implications of these types of hacks are. I would imagine that the owner of the devices could be sued for damages if they took down high profile sites. Any idea?
Hey Will, as someone who’s been following the evolution of Jigsaw very closely for a while now, this post was really awesome!
One thing I wonder about, is the impact of the constant pervasive question that most ask of Google- what it does with user data and the slightly more mainstream “does Google keep tabs on what I’m searching for?” This is a question that the founders have answered over and over again and I wonder about the kind of impact this might have on Jigsaw’s initiatives in terms of trust-building and data sharing concerns, and how willing institutions might be to partner with them in the light of the same.
Super fascinating post Will. I had no idea that this Mirai source code was freely available. Knowing that now, I’m surprised incidents like the October attacks are not more common. I’m glad to see that google is taking action and empowering others to do so with Jigsaw and Project Sheild, and I especially appreciated your assessment as to their incentives in doing so. It’s a great example of a company taking a long-game, holistic view of a problem, even when it is expensive and won’t show direct, short term payoffs.
I’m curious as to whether Google is also looking into the “coordination” elements of DDoS attacks. How does that coordination happen, especially at the scale we saw in November? Is it something Google can learn to identify and predict?
Great post Will, thanks for sharing! Like some of the posts above, I too am concerned about the potential for these kinds of attacks in the future. It’s great that Google has taken a leadership position in providing a free solution to certain groups, but what about related problems where Google is not strategically motivated to solve them? Are there any other organizations tackling those challenges? Do you think it’s something that can be solved in a free market economy, or is there a role for government action here? Overall, great post, thanks for highlighting this important issue!
Will, this was a very interesting post. I also looked at cybersecurity in my post, but I was focused much more on the hackers who spend an average of 229 days in a network while extracting as much information as possible. The DDoS attack model is terrifying in a different way, as it victimizes independent media sources rather than extracting information and data. I wonder if businesses such as Google can stay ahead of the ever-more complex and changing illicit cybercrime landscape. I hope that Google and root9B (my post’s company), among other businesses, continue to innovate and effectively respond to cybercrime.