#hacked: the proliferation of fake news bots on Twitter
Twitter supplies content to the news cycle through their highly influential social platform. But they are increasingly victimized by the dark side of technology: malicious bots. What should they do to protect their supply chain, their reputation, and the sanctity of news?
Twitter, a microblogging and social media platform, enables users to read and post short messages. But in actuality, Twitter has become a digital, real-time, public broadcast.
Today, Twitter is one of the main suppliers of 24/7 news updates. Because of digitization, user preferences have changed to active rather than passive and the news process flow has shrunk drastically. Consumers require information instantaneously, and they often don’t have time to read an entire article or watch a lengthy TV broadcast.
Through digitization, Twitter has allowed consumers to be more connected and more informed than ever before. But Twitter must pay close attention to cyber-security threats. Bots and hackers have learned how to outsmart Twitter’s systems, exposing weaknesses in their supply chain. On October 30th 2017, Twitter executives testified before Congress on the bots and misinformation that influenced the 2016 U.S. Presidential election.
Furthermore, the President of the United States uses Twitter as his preferred means of communication. This matters because Twitter’s user base is growing: from 310 monthly average users in January 2016 to 330 million monthly active users in October 2017 [1].
Twitter’s mission statement is “to give everyone the power to create and share ideas and information instantly, without barriers.” But at what cost?
Tweet, Sleep, Repeat – Twitter’s Supply Chain
From the end-user perspective, Twitter pushes content to users based on who they follow, their location, and what is “trending.” Users select which accounts to follow and can elect to turn on their location services, then Twitter’s algorithm pushes “trending” content to their Twitter newsfeeds. The algorithm identifies topics that are popular in real-time. For instance, if there is a 10-car pile up on a highway nearby, users can go onto Twitter and see an update on the crash via the Trending tweets. Or in cases of severe weather power outages, users can go on to Twitter to find the nearest shelter.
From the journalist perspective, Twitter provides 24/7 monitoring of the worldwide news [2]. Since users now want to consume news immediately, rather than the next day, journalists can use Twitter to stay on top of the news cycle and be the first to break a news story. Journalists can also provide raw materials into the funnel. Twitter then provides worldwide news coverage of journalistic stories. If a journalist tweets about a story that ends up trending, it can attract thousands of new readers or followers.
The looming threat to Twitter lies in the legitimacy of their site content. How does digitalization exacerbate this issue? Hackers continue to outsmart the Twitter systems with new technologies. Twitter users can have full anonymity through their elected username, so hackers can theoretically make thousands of Twitter bot accounts, have them all spew out the same fake news or hate speech, and cause a topic to become “trending.” Samuel Wooley, the director for research at Oxford University’s Computational Propaganda Project calls this “manufacturing consensus.” [3]
#QualityControl
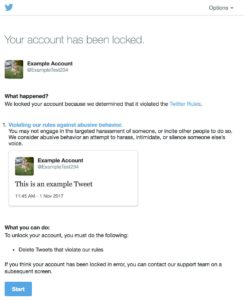
Twitter’s mission statement appears to be in direct opposition to fact-checking, but their reputation depends on a certain level of quality control. Twitter has been actively updating their policies around reported content and abusive users (Exhibit 1).
They have several systems in place that work to identify suspicious users, but often these systems are implemented retroactively.
- They have dedicated teams who work on protecting the quality of the tweeted information by reviewing flagged content, deleting malicious content, and suspending suspicious users [4]. (Exhibit 2)
- They are utilizing machine learning and automated processes to identify propaganda bots and automated log-ins. “These techniques now help us catch about 450,000 suspicious logins per day.” [4]
- They have a system to identify suspicious bots on mobile phones that exploit innocent Twitter accounts [4].`
Still, the cyber-security problems persist.
@TwitterSafety, here are my recommendations:
In the short term, Twitter should act fast and make quality content their number 1 priority. They should update their mission statement to include their commitment to the quality of the content they feature.
Additionally, they should focus on perfecting the filters in their process flow by utilizing machine learning and AI to supplement the dedicated compliance teams. In the long term, they should strive to have machines handle the entire process of filtering out malicious bots and content.
Lastly, they can work on implementing a system that incentivizes users to flag and report content – at the moment users are not empowered to do so.
Open Questions for discussion:
- Should Twitter be held responsible for the impact of the content on their platform?
- How should Twitter weigh the risks of alienating their most active and followed users with the reputational risks of inaction?
- How many controls are too many in the name of freedom of speech?
760 words
Exhibit 1
Exhibit 2
[1] Statista, “Twitter: number of monthly active users 2010-2017”, 2017. https://www.statista.com/statistics/282087/number-of-monthly-active-twitter-users/. Accessed November 2017
[2] Poynter, “I studied how journalists used Twitter for two years. Here’s what I learned.” March 22, 2017. https://www.poynter.org/news/i-studied-how-journalists-used-twitter-two-years-heres-what-i-learned. Accessed November 2017
[3] Wooley, Samuel. “Computational Propaganda in the United States of America: Manufacturing Consensus Online,” Computational Propaganda Research Project Working Paper No. 2017.5, 2017, http://comprop.oii.ox.ac.uk/wp-content/uploads/sites/89/2017/06/Comprop-USA.pdf, accessed November 2017.
[4] Twitter PublicPolicy, “Update: Russian Interference in 2016 US Election, Bots, & Misinformation, ” Twitter Blog(blog)), New York Times , September 28, 2017, https://blog.twitter.com/official/en_us/topics/company/2017/Update-Russian-Interference-in-2016–Election-Bots-and-Misinformation.html , accessed November 2017.





Thank you for your insightful discussion on the topic. I believe Twitter should only be held responsible for the dissemination of information that directly encourages violence. That responsibility, without question, ought to fall on all parties involved – governments, corporations, news media and individuals alike.
Other metrics – such as content accuracy or quality are often subject to the interpretation of the viewer. How can one rely on a corporation to police such metrics without introducing bias? As we have seen, similar platforms to Twitter have struggled with this in the very recent past (https://www.washingtontimes.com/news/2016/may/23/facebook-admits-rogue-employees-may-have-shown-bia/)
In today’s hyper-polarized world, one cannot rely on humans to police each others’ content. Leave it with violence – one thing most of us can agree on must avoided at all costs – and allow people to make up their minds regarding accuracy or quality of other content.
Twitter’s power comes from its users, particularly the influential ones who post thought-provoking, funny, or relevant tweets. It is this active user base that encourages others to either actively or passively use the platform. However, as the caliber (and even authenticity) of the user base is put into question, the reason to check Twitter or tweet diminishes. It is therefore critical that Twitter address the inauthenticity and danger of hackers and bots. Whether or not Twitter believes they are “responsible” for the content on their platform, low quality and questionable content will negatively impact their business. Further, the court of public opinion will ultimately hold Twitter accountable for the content on its platform. To combat these risks, Twitter should institute a more rigorous sign up flow that authenticates users and verifies them before they are able to tweet. While this may create hurdles in the signup flow, Twitter is already established and widespread enough that it likely will not have an outsized negative impact on their business. In addition, at this point in Twitter’s company lifecycle, it is more important for the company to ensure “real” users than to allow for unchecked user growth at the expense of the user quality. Twitter also needs to have a continuous due diligence process that maintains standards for content and consistently monitors suspicious account activity. While freedom of speech is an inalienable right, Twitter is a business that has the right and obligation, to its users and shareholders, to ensure the validity of its content.
Excellent topic and text – fake news have become increasingly critical on these last few years, and yet no definitive solution arose.
I believe Twitter should feel accountable for fake news, even if they avoid legal obligation to what is shared on their platform. Their business model requires trust and authenticity, so I agree that quality should become their #1 priority. I see the quality issue with 2 different types of solutions: anticipating fake news to avoid their publishing, and quickly reacting to fake news and removing the content from Twitter (this can be compared to preventive and corrective medicine. The first is much more effective and cheap, yet sometimes diseases are unavoidable, and corrective treatment is required).
Anticipating fake news means imposing barriers to the “freedom of speech” they preach, which might also impact their business on the short term, but is critical for long term survival. This might be done either on the signup, or every time a user posts. To reduce the impact on “freedom of speech”, verification should be focused on signup. It is the most effective way to a more trustworthy platform, and should be prioritized versus correcting. If there is a way to ensure 100% authenticity on the user database, then all other actions will be much less important, although still useful to deal with exceptions (for example, login theft). Not an easy solution…
Love this topic! My main question regarding this topic is if one holds Twitter, or other platforms, responsible for the content, or if one believes that these platforms have a responsibility to police its content, how would they do so? Certainly, the FCC has traditionally regulated speech on television to a moderate degree, though this has been reduced in the past few decades. One could argue that large internet platforms could be brought inline with the existing regulations for TV broadcasters. Yet, the logistics of doing so are of an unimaginable scale. There are more than 500M tweets a day on Twitter. Even if the vast majority would not fall under any scrutiny, how could Twitter possibly police its entire platform? Automation can only do so much. Nefarious trolls and bots are a dime a dozen. Any tweets deleted, accounts closed down, can reappear instantly under different and new accounts. Reporting functionality can be easily abused by similar, leading to an extraordinary amount of human review necessary. The only plausible way to reduce bots and trolls is to increase the friction of opening accounts or posting tweets, but increasing such friction would also lead to a massive reduction in the real user base of the platform. Meanwhile, Twitter would not be able to hire enough humans to keep up, the cost would be astronomical. This is especially true when some of the nefarious actors are nationstates with far deeper pockets than any private company.
Personally, I believe something definitely needs to be done, but I am not sure there is a reasonable solution in the near future. One day, AI will be advanced enough to do the job of humans in this capacity within an acceptable amount of false positives, but that is not today.
This is a great take on the digitalization of news! I do believe that Twitter must take responsibility for the content on their platform. Anything that is posted, even if the content creators are not controlled by Twitter directly, are implicitly being backed by the company. The users and readers are aware that Twitter has control over blocking users, and thus, Twitter makes a statement with complicit inaction if they do not police the content. Furthermore, given the wide reach of Twitter content, I believe that regardless of reputational risk, Twitter must take a stance on fake news given their influence on the media ecosystem and broader society.
While I do believe in freedom of speech, this method of speech is intentionally deceitful. The news pieces are not stated as opinions or satires, but instead as fact. This misrepresentation diverges from what freedom of speech is meant to protect. The controls implemented by Twitter should primarily be aimed at controlling the false statements, as opposed to silencing opinions that may not be popular.
Really interesting write-up on a really interesting topic!
Twitter faces a bit of a peculiar situation here: its “supply chain” of posts and news is created and curated by the company’s users, and the sites network effect creates the company’s “product” (the posts that appear on users’ feeds), and through this, the company’s value. But at the same time, the most existential threat that Twitter faces is driven by an over abundance of this same “supply”! This seems absolutely bizarre. With that said, when taking a step back and just thinking of the tweets as a product in a more traditional way (e.g. as a crate of blue wine vs. as a bit of data), it actually makes sense – similar to other companies, Twitter must to take steps to ensure an unspoiled supply chain.
As noted in the above comments, tackling this issue will not be a small feat. It will be incredibly challenging both in terms of the technology and human judgement that will be required. However, given the critical nature of the problem, and its potentially all-reaching impact on Twitter’s “supply”, it’s one that the company can’t reasonably ignore.
Twitter’s core competency is not filtering content and certifying its legitimacy. Rather, Twitter’s customer promise is to facilitate communication easily among its users. As such, Twitter should not attempt to restrict the comments on its site, and they should leave verification of news to groups that specialize in this such as journalists and news outlets. Moreover, adding in a layer of content verification will increase the lead time to publishing tweets. Many are choosing to announce news through Twitter for precisely the fact that it is a very quick way to get news out to the public. Twitter could, however, educate its users on the fact that it does not support the views on expressed on its platform nor verify any message accuracy.