Fireeye on the prize: helping other firms navigate digital transformation securely

Fireeye has become a winner by helping firms navigating digital transformation win in the ongoing war against cyber criminals and advanced persistent threats.
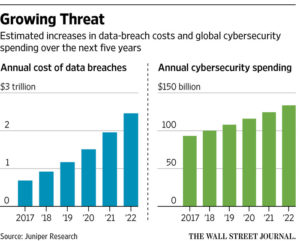
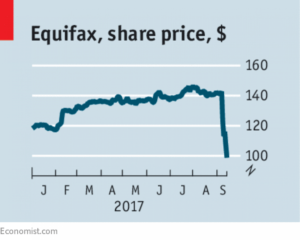
The premise of our course is that “the digital revolution is rapidly transforming the fundamental nature of many companies in a wide range of industries” — this premise necessitates technological innovation to stay competitive relative to traditional and upstart peers, but that innovation comes with a particular risk which executives are not used to managing: the threat of cyber/ information security breaches and attacks. As a broad range of firms seek to digitize, and in the process of doing so expose themselves to new threats (e.g., the annual cost of data breaches is expected to grow to nearly $1T in 2018), cybersecurity firms like Fireeye have become winners (e.g., as annual cybersecurity spending approaches $100B). High profile, poorly managed breaches such as the recent Equifax breach (see effect on share price below) have only underlined the need for security to other companies, as value can be quickly destroyed when cyber prevention and response are mismanaged. Since most firms lack these capabilities in house, they are turning to companies like Fireeye to provide them.
Fireye creates value in several ways:
- Products: provides a full suite of products for detection/prevention, analysis/response, and for security operations
- Services: Mandiant consulting arm provides threat response capabilities and intelligence
- Solutions: develops customized solutions for specific needs
The product and solution spaces are fairly crowded with other firms — where Fireeye really sets itself apart is in the services space, which conveniently is likely one of the higher margin areas of the business. Fireeye’s acquisition of Mandiant Consulting in 2013 was a coup from both a marketing perspective and from a fundamental business valuation perspective. Mandiant threw itself onto the map by providing the first detailed private sector attribution of an advanced persistent threat (APT) or state-backed threat, pointing the finger at China in an intelligence report with exceptional forensics (see youtube on APT1: China PLA threat detection below). Fireeye benefitted from the initial halo generated by Mandiant for providing this public benefit analysis, and continues to benefit from Mandiant-published thought pieces as they attract customers to the firm who then buy Fireeye’s products, services, and solutions. Fireeye’s services division (of which Mandiant is an integral part) has also become one of the first calls for governments (e.g., OPM) and firms in the wake of serious cybersecurity incidents to help with threat analysis and mitigation; willingness to pay in the midst of these incidents is high — CEOs now undestand that their own jobs are on the line should an incident be poorly managed — and Fireeye is able to (a) drive up WTP higher than its peers, and (b) presumably capture more WTP than peers due to its track record and thought leadership (i.e., what it calls an intelligence-led approach).
Video of Mandiant’s APT1: China PLA analysis: https://www.youtube.com/watch?v=6p7FqSav6Ho
The need for cybersecurity products and services is rapidly growing, but so is the competition to provide those products and services. To remain competitive, Fireeye would benefit from continued public thought leadership/ demonstrations of its analytical prowess — as a form of marketing, this approach has set Fireeye apart from its competitors who focus on online and airport ad buys. This type of analysis also provides a public good, raising the awareness of executives and deterring bad actors through public attribution. As our society continues to undergo a significant digital transformation it is much more desirable that the “losers” be the cybercriminals and state-backed actors who seek to exploit that tranformation for their own ends; Fireeye has the potential to help firms navigating digital transformation to be the winners, while sharing in some of the value created by those companies to be a winner itself.
[1] DIG-IT Canvas
[2] WSJ: The evolution of a cybersecurity firm. https://www.wsj.com/articles/the-evolution-of-a-cybersecurity-firm-1494986640
[3] Economist: The lessons of equihack. https://www.economist.com/news/leaders/21728894-security-breach-equifax-was-handled-spectacularly-badly-other-firms-take-note
[4] Fireeye website: https://www.fireeye.com/products.html
[5] Youtube: Fireeye APT1 identification. https://www.youtube.com/watch?v=6p7FqSav6Ho



The cybersecurity space is certainly a fascinating space, but I think the winners are losers here are going to be hard to call. Already, the space for enterprise-level cybersecurity solutions is relatively competitive. The traditional security firms (e.g., Symantec, Intel McAfee) have begun to seriously refresh their offerings, large enterprise software conglomerates have instituted new initiatives to stem share loss (e.g., Oracle), there is a host of other billion dollar public next-gen security companies (e.g., Palo Alto Networks, Check Point, Fortinet) that have taken significant strides in the market, and a tremendous number of highly valued private startups (e.g., Okta, Ping) trying to carve out a space in the cybersecurity market. Ultimately, cybersecurity is such a fragmented and fast-moving space that the winners of yesterday could easily become the losers of tomorrow. Even FireEye has had its fair share of challenges. In 2014, coming off the highs of their acquisition of Mandiant (great decision, which you write about), the stock price hit over $85 per share. Today, the stock is at $15 per share as it has faced growth challenges and product competition from the likes of Palo Alto and Check Point. In this space, it’s always faster, better, cheaper wins, and that places huge R&D pressure on all of these companies.
Thanks for sharing JPW and I agree with JLuos’s comments above. I think we are coming into an an age where developer’s are now being forced to think about security when innovating. Although security is typically not the first (or second or third) thing engineer’s think about when creating products, the series of security breaches over the past few years are now, thankfully, forcing companies to focus efforts on security in the hybrid and multi-cloud environment. I was fortunate to intern with a cloud security solutions start-up this past summer and the field is fascinating… and evolving very quickly. From everything from bare-metal servers to the software container space, there is still surely room for innovation.
It is great to see Fireeye succeeding in the space, especially in the services area. I think a critical aspect of Fireeye’s future performance will be its ability to acquire talent and potentially smaller start-ups working on evolving threat issues. It will also be interesting to see how Fireeye adapts to regional regulation around the world and whether it chooses to get involved in issues such as GDPR or stays focused on its core business.